- | 9:00 am
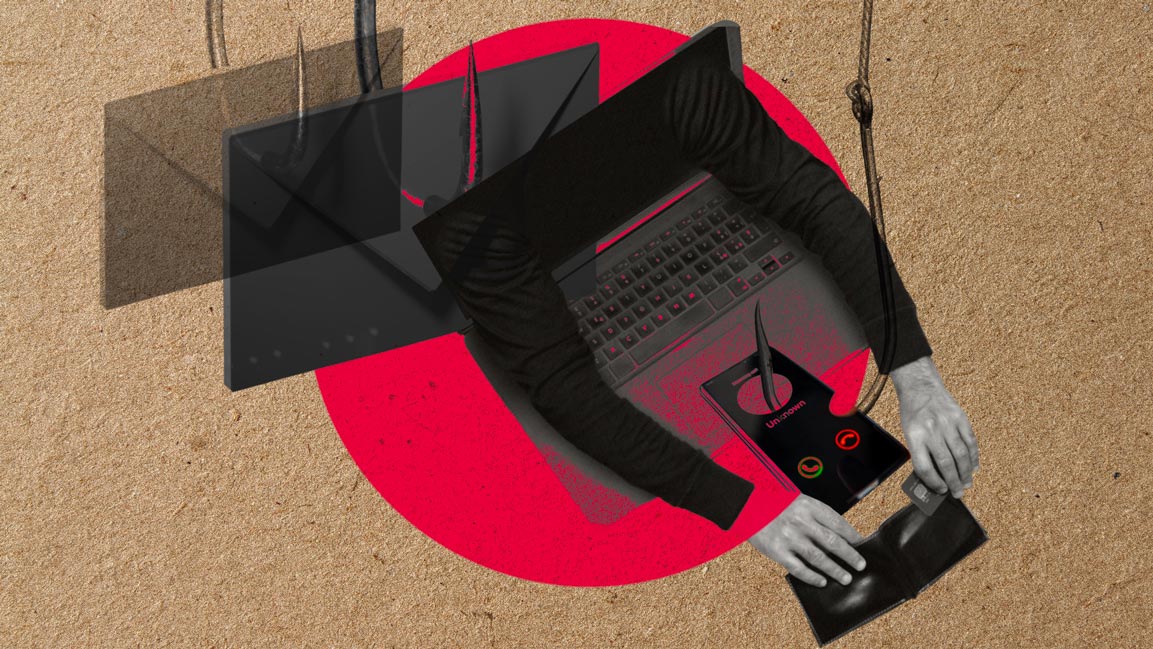
These scams are timeless. Are technology and social trends making them more dangerous?
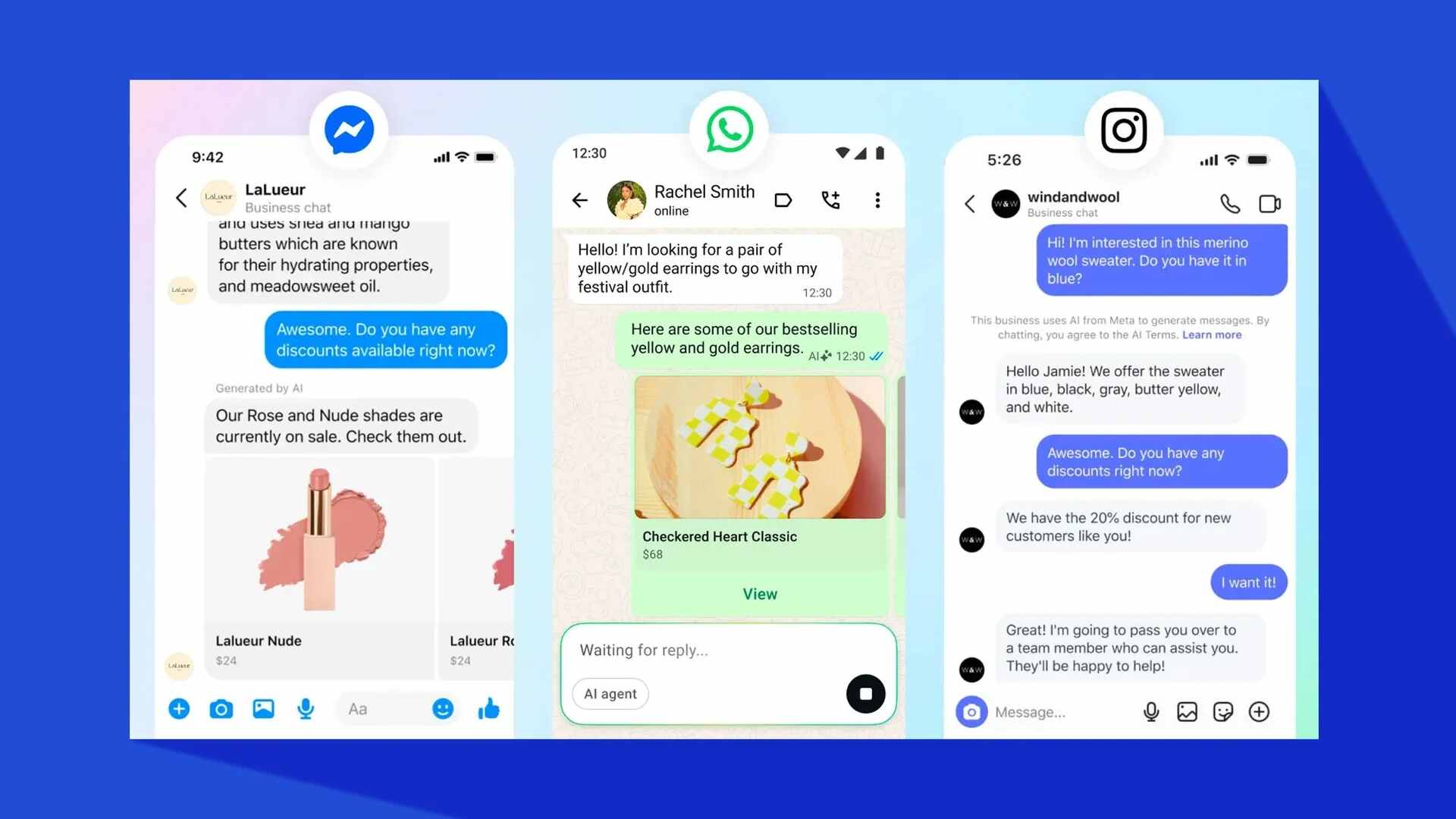
With social media turning into a goldmine for scammers, a few questions need to be answered.
It was back in 2019 when questions about the worth of Instagram influencer Ramon Abbas started cropping up. The extravagance showcased in his social media feeds bedazzled followers. Then, in June 2021, in an interesting twist, people woke up to the news of his arrest for online fraud.
The influencer, and his gang, would send out emails, almost identical to legitimate companies, to target customers of those companies to divert payments to themselves. A cyber-scam and fraud worth approximately $1 billion were busted. Such scams are increasingly becoming common.
With the emergence of new technologies and social trends, Saeed Ahmad, MD at Callsign, Middle East, notes that these are old frauds, albeit with new twists.
“Consumers are easily tricked into giving away personal information, and businesses rely on passwords and usernames, supported by OTPs via SMS. These are no match for fraudsters as they can easily circumvent them through the credential stuffing, SIM swap, or SS7 attacks,” he says.
Passwords and possession of a mobile phone don’t prove one is the genuine user trying to access the account, so scams to achieve ATO continue to evolve. “These scams continue to proliferate globally, and MENA is not immune,” Ahmad asserts.
In 2021, Group-IB Digital Risk Protection (DRP) analysts identified a fraud scheme targeting users in over 16 Arabic-speaking countries. As a part of their attacks, the scammers abused more than 130 well-known brands. The criminals posed as famous brands from sectors such as telecommunications, retail, and entertainment, offering gifts and lottery games purporting to be recommended by celebrities.
In total, the analysts discovered more than 4,300 fraudulent pages created on Blogspot, a popular blogging service.
EXPLOIT HUMAN FEARS AND EMOTIONS
Yakov Kravtsov, Head of the Digital Risk Research Team at Group-IB, says that while all scams are fundamentally similar, they exploit human fears and emotions. What changes, though, are the technologies the scammers use. “Scammers most often use big-name brands to their advantage. Impersonating them allows people to drop their guard. Just as the monitoring and blockage methods evolve, scammers constantly come up with new technology to evade detection and increase the success rate of their fraudulent operations,” adds Kravtsov.
Another recent example is the so-called targeted links tailored to a specific victim. Such links can be opened only once, complicating the detection and inevitably leading to the scam’s longer life cycle, thus hampering the takedown and investigations. As a part of the targeted links scams, cybercriminals exploited nine brands from Bahrain, Qatar, Oman, Kuwait, and the UAE.
“Globally, cybercriminals mostly try to exploit the brands of leading telecommunications companies, which enjoy special ‘love’ in this scheme, and make up more than 50% of the total number of brands exploited, followed by eCommerce and retail,” says Kravtsov.
According to a recent Kaspersky survey, 65% of respondents in the United Arab Emirates highlighted that they or their loved ones suffered online crimes via social networks.
From digital blackmailing to fake recruitments, scammers have leveraged social media and technology in more ways than we know.
“A scammer asks an unaware user to provide a six-digit number that the user received supposedly by mistake. Once the fraudster gets the six-digit number, he can hijack the user’s WhatsApp/IM account. The scammer can then access the user’s contacts and send them IM messages asking for money, known as digital begging, which is becoming commonplace these days,” reveals Maher Yamout, Senior Security Researcher at Kaspersky.
Yet another tactic is when a scammer possesses a local SIM card from a particular country, changes the IM profile picture to the local country’s central bank logo, and sends messages to many users in the local language. This is done to trick them into sending money, contending that their bank won’t block their accounts if they do so.
HOW SCAMS THRIVE
Moreover, Yamout reveals that social media and phishing are used intensively to refract a fake recruitment scam wherein an unaware user receives an email from a phoney company mimicking an authentic organization and tells the user that his profile matches a job description.
“The scammers provide all information in the email with signatures and the fake company website URL. After the victim falls into this trap, they take personal information from him. They ask the user to pay for a one-way ticket through the scammer’s travel agency where they charge a higher amount, and the visa never comes,” he explains.
According to Kravtsov, poor cyber hygiene and low awareness about possible deception methods make these scams thrive. “We need to investigate scams and bring such cases to authorities to make the perpetrators accountable,” he states.
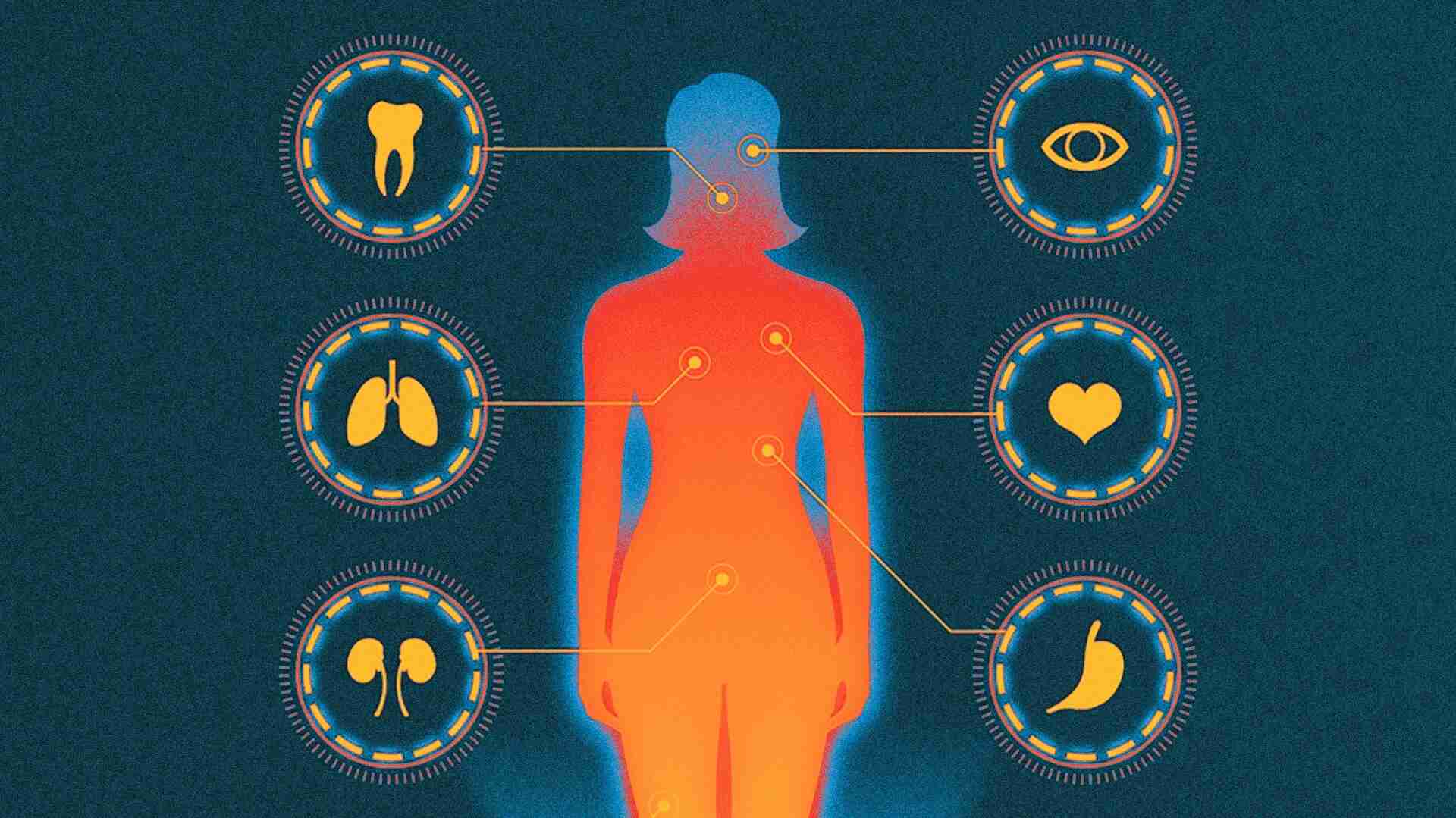
Now, technology can identify individuals through their unique behavioral traits. Threat detection helps individuals safely access online accounts, which is crucial in locking fraudsters out.
While darkness engulfs this space in technology, there’s also hope if embraced more smartly. Ahmad contends that organizations need to update outdated analog technology that has been repurposed for digital applications. “Companies need to rethink their authentication processes for the new digital world we live in today,” he says.